Stefano Pallicca - 9 novembre, 2021 - 5 ’ read
Stefano Pallicca - 9 novembre, 2021 - 5 ’ readVoice Analytics: designed for your privacy and security.
Security first and foremost.
Here at Imagicle, we made the Cloud a core part of our business. To be able to provide our customers and partners with the high-touch Cloud services they expect and deserve, we made security our north star. Not only do we develop our applications following the Secure Software Development Life Cycle Approach, but we’re also partners with Amazon AWS (among other leading cloud providers, like Azure), which requires top-level security as one of the five pillars of its well-architected framework.
Security is the core of everything we do, and we’re always committed to doing better every day. The last major acquisition, for example, was the ISO 27001 certification, which covers the whole company and its processes and is focused on risk assessment and prevention.
More about that on our security page.
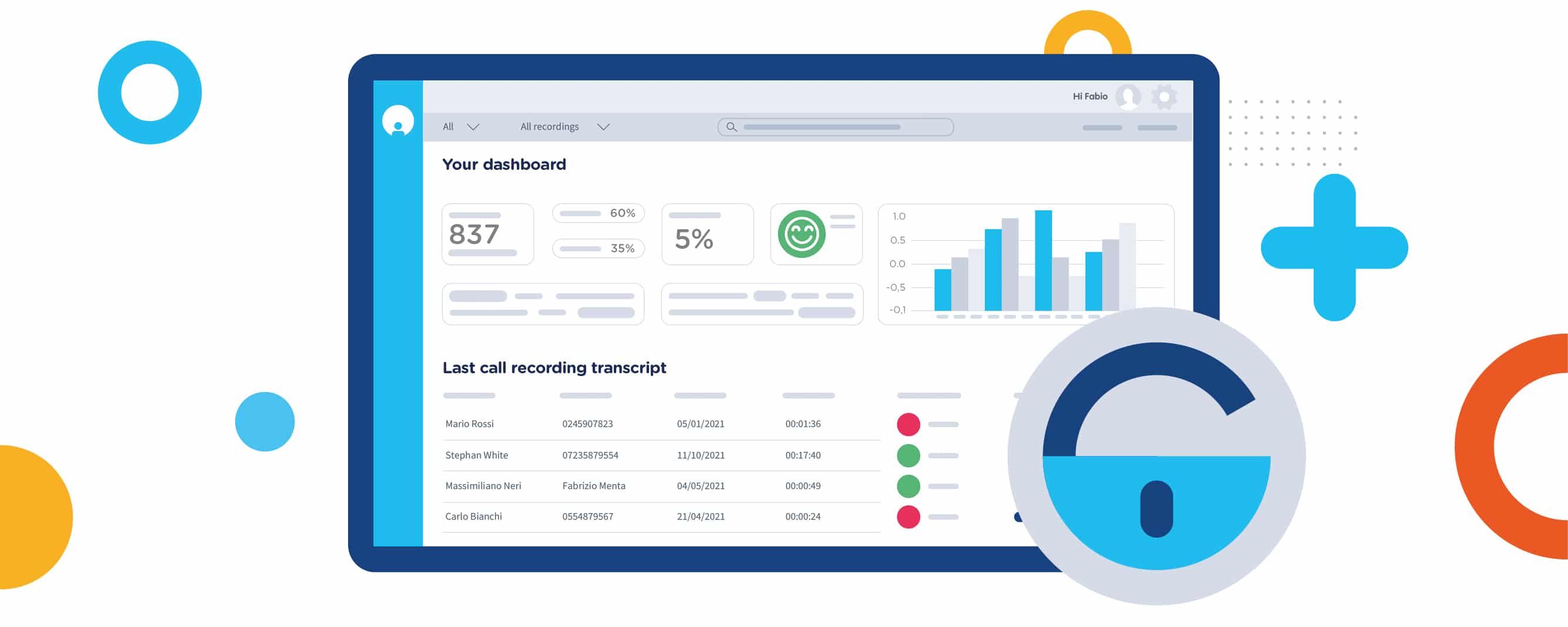
Let’s now dive into the key features that we implemented in Voice Analytics to give it the most solid security. But first, if you need to catch up on what Voice Analytics is in detail, this is the article you’re looking for. Otherwise, watch this out 👇👇👇
All-round protection.

Cloud security and availability.
Imagicle Voice Analytics spans multiple AWS regions and relies on multiple availability zones to ensure that a failure in a single data center, should it happen, would have no impact on the product’s functionality or the availability of our customer data.
Customer data is automatically replicated among different availability zones in the same region to avoid losing data due to a failure in the data center. Moreover, it is protected against accidental deletion, allowing us to recover it from unintended actions or application failures.
Network security.
Our network security spans different layers. We have separate environments for development, staging, and production, with limited connectivity between production and non-production environments. Production data isn’t replicated outside the production environment.
Each environment hosts a virtual private cloud (VPC) with separated services; white-lists and specific firewall rules allow services to communicate with each other. To limit the access from the public network to our services, we use a Web Application Firewall (WAF) to protect our applications against web exploits, DDoS attacks, and bots that may affect the availability of our services.
Data security.
Keeping personal data secure is a shared responsibility. As long as your information is on your PC, you are responsible for keeping it safe. But as soon as your data leaves your computer, both while in transit and when staying in our data centers, we are in charge of taking care of its security.
While in transit, any data exchanged between a client and our Voice Analytics platform is encrypted. When traversing public networks, it leverages TLS 1.2 and higher versions, the industry-standard security protocols designed for web applications.
In our data centers, customers’ data, i.e., the recordings and the content of their transcriptions, is encrypted at rest using the AES-256 standard, and only the owner of that data can decrypt it.
To simplify our daily job on cryptographic matters, we rely on AWS Key Management Service (KMS) to manage cryptographic keys used to encrypt and decrypt customer data.
Having a trusted partner with strict security procedures means we can sleep soundly at night, and that’s very important to keep rocking with our apps! 😉
But it’s not only about data encryption. We work hard to meet business security requirements and help our customers and partners prevent avoidable fines. Proper authorization controls, role-based access, detailed reporting features, flexible data retention, and High Availability with disaster recovery are just some of the security measures implemented in our apps, ready to meet a broad set of international and industry-specific compliance standards such as GDPR, MiFID II, FINMA, PCI-DSS and more.
Tenant isolation.
Our cloud infrastructure is shared among our customers (our tenants). This way, we can deploy patches and bug fixes once for all customers and our deployments are always in sync. Nevertheless, customer data is separated; that is, other customers cannot access your data. Your data resides physically with other customer data, but it’s logically separated from it.
Please take a deep breath and read it again.
Yes, you read it right!
If you did not faint, read on, and discover how we managed to keep security and segregation, despite relying on a shared pool of resources.
Let’s make a real-world example: before accessing Tenant A‘s data, a code puts on a “Tenant A magnetic badge” and swipes it in a virtual badge reader; Tenant A’s door opens and the code can access Tenant A’s data. If the same code swipes this “magnetic badge” in Tenant B’s door, it remains locked out.
In conjunction with KMS (see above), this mechanism lets us encrypt each tenant’s data with its key. As introduced before, this is how Tenant A can decrypt all and only its data and none of Tenant B’s data.
Accidental errors? No thanks. 😉
A very welcome consequence of implementing tenant isolation is that our architecture prevents accidental errors, which might give access to someone else’s data. Any unauthorized access caused by a programming error or a bug in our code is ensured to be blocked at a lower level, before trying to access the data.
Thus, a triple-level of security:
- Tenant A and Tenant B are logically isolated.
- Developers have a safety net in case of accidentally introduced bugs (of course, this is not our case 🙂 ).
- Tenant A and Tenant B encryption keys are separate. In the remote case of Tenant A coming into possession of Tenant B’s data, Tenant A will not be able to decrypt it, making that data useless to Tenant A.
Compliance with laws and regulations.

As said before, Imagicle runs its business in compliance with several industry standards and regulations, such as ISO 27001 and GDPR. Providing our customers with a security program that meets their requirements in terms of expected security and compliance is a top priority for us.
Compliance and regulatory requirements such as GDPR and PCI-DSS play a vital part in any business managing customers’ data nowadays. Imagicle Voice Analytics can help make sure agents stick to any requirements and can also prompt them about disclosures and other requirements, which can help you avoid potentially costly litigation.
Visit our compliance page to learn more about our certifications and security protocols.
What’s next?
To conclude, we’re very proud of how Voice Analytics turned out, from UX to functionality, to the core of this article: security. But we never stop wanting more. In our daily effort to make things better, we implemented monitoring solutions that trigger an alarm in case something bad happens, such as application failures and suspicious activities. More importantly, we are implementing alerts that can be triggered before something bad happens to act proactively and prevent the accident. In other words: you can lay your head to rest because if there’s an issue with your Voice Analytics solution, it will be solved before you notice it’s there.
As you see, we take security as a serious matter in Imagicle, and keeping customer data safe is a core part of our daily job.
Wanna see our Voice Analytics in action?
Register for the dedicated webinar and enjoy a live demo.
Wednesday, January 26, 11,30 AM
Vous pourriez également être intéressé par...
-
Products BlogCloud, Manager Assistant, Voice Analytics: a brand-new Imagicle world.New products to enhance your work, new integrations to make it easier. From the Cloud or from the ground, dive into the latest Imagicle news with our co-CEO and CTO.
-
Security BlogISO 27001. Taking care of your data protection.Imagicle obtained the ISO27001 certificate. Here’s a summary of what it means and what will change in terms of security.
-
Products BlogVoice Analytics: AI and use cases to elevate customer satisfaction.Introducing Voice Analytics, a cloud-native AI service unlocking the real power of the content of phone conversations.